Considering that one of the largest DMOs in the country was hacked by the Russian ransomware group LockBit and their entire network data stolen, there has been surprisingly little media coverage about this massive data theft. The consequences of identity theft to the millions of MCNA clients, mostly children, are mind-boggling. Look at this recent article about the consequences to students of a school that was hacked. Even the ADA was hacked.
More than just PHI stolen
But there is more. MCNA's refusal to pay the $10 million ransom not only exposed personal health information of some 8.9 million clients but all provider and state health agency information on their server. Also included are MCNA human resource files on their employees and probably information on their board which would include former Texas governor and Secretary of Energy Rick Perry.
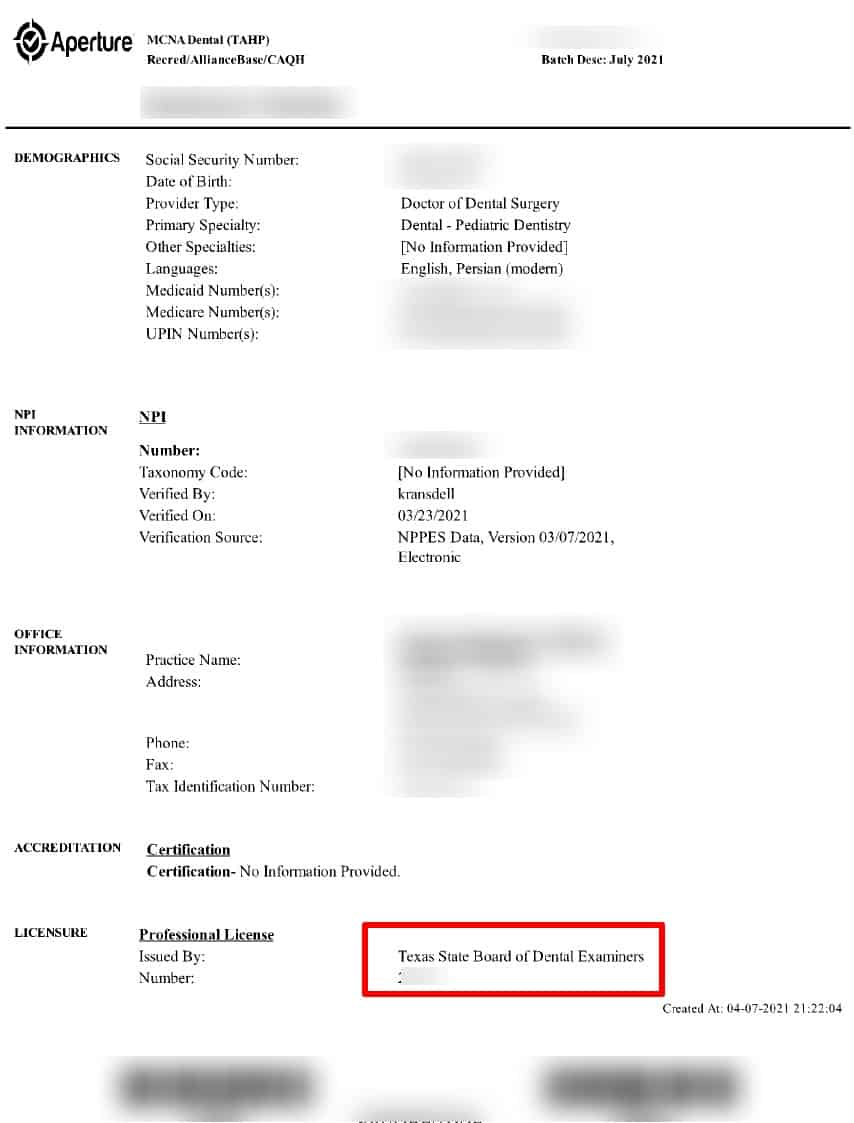
For providers, this apparently means their banking information, financial data, credentialing applications, audit results and correspondence, complaints, prior authorizations, etc. -- everything MCNA has on them including MCNA's internal correspondence. We are talking about every provider nationally, past and present, not just in Texas. Their practice data is compromised.
Working with security analyst
We know this because we have a screenshot of the MCNA server directory structure plus we are in possession of some of the documents taken. The directory structure is not impressive with titles like "Meghans Super Top Secret Folder" and "New Folder."
TDMR has been liaising a security professional with the Louisiana-based NOIT group, to assess the damage done by this incredible leak. Ms. Baker was the first we are aware of to post online about this hack back on March 29 when LockBit first announced the hack on their dark web portal.
Texas HHS has been remarkably cavalier about this with OIG posting a one-sentence notice on their website.
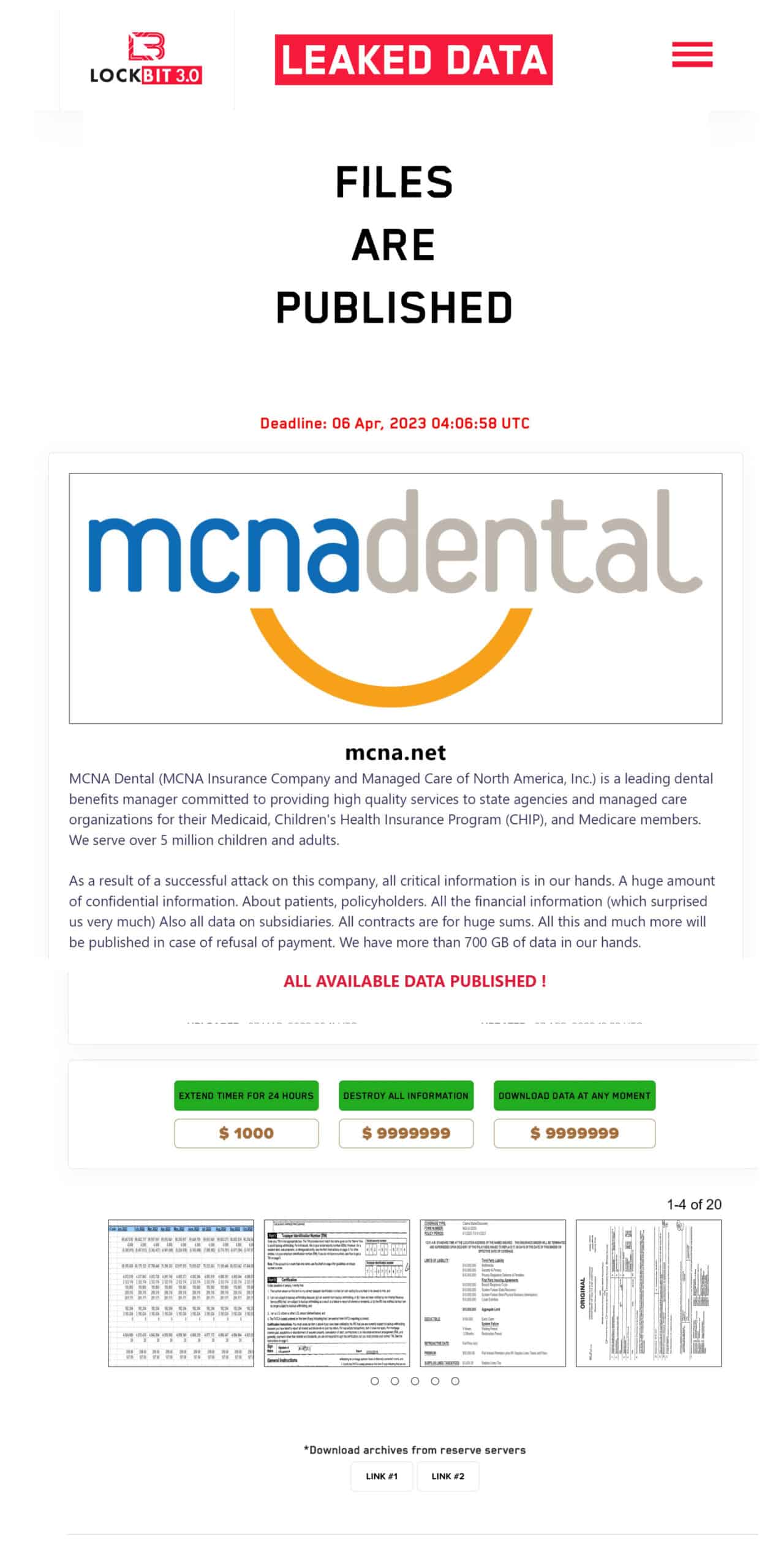
Russian hacker group
LockBit is a Russian hacker group based in the Netherlands. Their dark web portal says, "It is forbidden to attack the post-Soviet countries such as: Armenia, Belarus, Georgia, Kazakhastan, Kyrgyzstan, Latvia, Lithuania, Moldova, Russia, Tajikistan, Turmenistan, Uzbekistan, Ukraine and Estonia. This is due to the fact that most of our developers and partners were born and grew up in the Soviet Union, the former largest country in the world, but now we are located in the Netherlands."
Lockbit demanded a $9,999,999 ransom in Bitcoin which was not paid and the server data, some 764 GB, was made available for other hackers to take and use on April 9.
Data currently not in Lockbit archive
We note that this MCNA data does not appear to be on LockBit's portal archive now. So perhaps MCNA has now paid the ransom or the former US Secretary of Energy used his influence. MCNA has not responded to our queries.
Safeguarding your practice tips
Ms. Baker offered these security tips for providers to follow to ensure their information is not used to hurt them.
1. Identify the data leaked - Once the leaked data is identified, the provider may then be in a position to insulate themselves from further compromise by moving quickly to alter or disrupt the information. For instance, if a bank account number was leaked, changing bank account numbers may not be sufficient if other data like the Federal Tax ID number or Social Security Number of the provider was also leaked. To disrupt the information, I'd suggest opening an account at another institution entirely. Other options such as using Treasury Management Services and Positive Pay, would be an additional level of protection.
2. If the provider has Cyber Insurance, reach out to the insurer. As a part of most policies, insureds can be provided a breach coach. Consult with the provider or breach coach to discuss concerns related to the MCNA breach and see what resources or suggestions may be available.
3. Insist on Security Hygiene – Think of a password like a toothbrush. They should be used often and not shared. Everyone should use their own password and no one should have access to shared passwords. Passwords cannot be reused in multiple places. Each account, business and personal, should have their own unique password. Investing in a password manager for each staff member is relatively inexpensive and runs $1 - $3 per user / per month.
4. Implement Zero Trust Framework - Implementing a Zero Trust framework can be accomplished with minimal to no expense to the provider. It requires every user or device account be protected by multiple layers or factors of identification. For maximum protection, include all third-party accounts and access.
5. Monitor entry and exit points – Just like watching the front and back door of a provider's physical office, it is equally important to watch the digital entry and exit points of their network. This is best done with a commercial router configured with intelligent and secure routing. Avoid residential or SOHO options, as they lack the advanced protections and log monitoring needed.
6. Endpoints – Servers, laptops, workstations, and IoT devices should be protected with a next-gen antivirus product and reviewed for vulnerabilities, missing updates, and patches. Any deficiencies corrected as efficiently as possible. There are many commercially available tools to accomplish endpoint management. Since most endpoints in dental offices are Windows-based, the most efficient and least expensive method to get both antivirus and endpoint management is Microsoft Defender.
More to come!
LOCKBIT PORTAL NOTICE WITH RANSOM AMOUNT
(to view larger versions of these documents, right click and open images in a new tab)
MCNA SERVER DIRECTORY

TEXAS PROVIDER CREDENTIALING DOCUMENT (blurred)



Thank you for this excellent article It was very helpful and informative.